What is Data Center Network topology?
A Datacenter network topology is the combination of Data Center resources including computing power, storage, and networks that make up your data communication network. Datacenter networks are one way you can easily connect to thousands of servers, to manage the demands of your cloud computing network.
Before we get into it, let’s keep in mind what a datacenter is…
What is a Data Center?
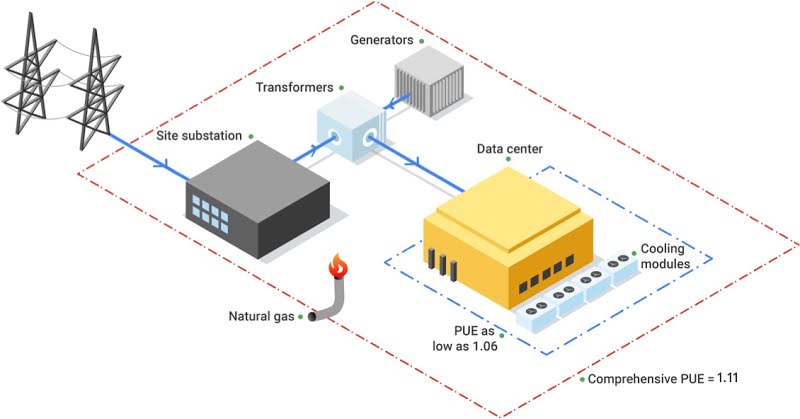
A data center is a place or building set aside to manage the storage of computing systems and associated or interconnected components and devices; such as telecommunication devices, routers, and servers, and storage systems. All data on the internet gets stored on a server and remains accessible round the clock.
Types of Data Centers
The Data centers may differ in size; it can be one small server room or a group of servers in a larger warehouse.
The data center provides storage space to maintain various computing infrastructures and to connect with the cloud computing infrastructure. Remember that maintaining a datacenter consumes lots of energy. But it allows you to store your data and access it 24/7.
Note these four types of data centers:
Enterprise Data Centers
These types get built for a special purpose that makes them very useful in internal purposes of a single organization.
Colocation Data Centers
A co-location datacenter is a management space, within a larger data center, you rent for personal or business use and is in a remote location. The rental space provides the various resources of the data center that are available for the people.
Managed Service Data Centers
Management of this data center gets carried out by a third-party services provider and it offers different aspects of data storage, computing, and many other data management and computing services.
Cloud Data Centers
The cloud data center offers various types of services with the help of the third-party services provider and data and applications get hosted in cloud service platforms such as Microsoft Azure, Amazon Web Services, and Google Cloud Platform.
What is Network Topology?
A Datacenter Network Topology is simply the channels used to connect various nodes, servers, and computing devices to create physical and wireless network connections. It is the communication methods of the devices and telecommunication networks between various computing devices.
Types of Data Center Network Topology
There are multiple data center network topology types available;
Three-tier Data Center Topology
The Three-tier data center network topology uses the multi-rooted tree-based network topology, which involves the combination of three layers namely; access aggregate layer, core layers, and network switches.
Aggregate layer switches get interconnected to various access layer switches. And the core layer is used to create a connection for the data center to the Internet.
It’s efficient for enterprise-level network devices and it is very costly and power-consuming.
Fat tree Data Center Network
The Fat tree data center network is used to solve a basic problem with the three-tier data center network architecture. It uses the network switches-based architecture by using the Clos topology.
The fat-tree network topology also operates network switches to access the various layers, like aggregate and core layers. It uses more network switches rather than the three-tier data center network.
DCell
The DCell is a hybrid Datacenter Network. Here, one server gets connected directly to the other different servers within the same data center. The server in the DCell Network topology uses multiple Network interface cards.
This topology use servers and switches connected within the cell.
Core Components of a Datacenter Network Topology
The core components of the data center:
- Routers
- Switches
- Firewalls
- Storage
- Servers.
- Network infrastructure
- Computing resources
Conclusion
In this article, we have covered the important data center network topology types and the concept of the data center. I hope you have found this article helpful. Don’t forget to leave a comment below.