Recent years have seen a dramatic rise in Bring your device (BYOD) policies. Many businesses are now letting their employees use personal devices to complete work. Organizations save on operational expenses immensely by avoiding additional purchases of different devices.
Also, employees don’t have to share devices when working—a driver for productivity. Implementing a BYOD policy can be tricky. Businesses must trust employees to protect and maintain security within the company.
This article explains the essential steps of creating a BYOD policy that works. One that your employees will comprehend.
What Are the Benefits of An Effective BYOD Policy?
You must first understand the key benefits of a BYOD policy before successfully implementing one for your business. You must also prepare to answer questions and explain so that you’re not caught off-guard by your employees. Consider the following key benefits of allowing employees to use personal devices for work:
Enhanced Convenience
Life becomes convenient for everyone when employees no longer have to switch devices. It saves time and energy for employees and can even increase efficiency because they are already familiar with the device. It also makes BOYD efficient for businesses because they do not need to train users.
Cost-Saving
Implementing an effective BYOD policy encourages employees to use personal devices that are accustomed to them. It helps save costs of purchasing business equipment and maintenance fees for operational devices. Businesses can pay a small stipend to cover device maintenance costs and data plans instead of paying the total cost of ownership.
Enhanced Flexibility
Accessing information regardless of one’s location helps employees remain productive. BYOD gives people full-time access to their devices, and they can access information and collaborate quickly and effectively.
Updated Technology
Whereas organizations are less likely to purchase the latest devices upon release, employees can ensure that their technology remains up-to-date. It is easier for an individual to upgrade their devices faster than companies.
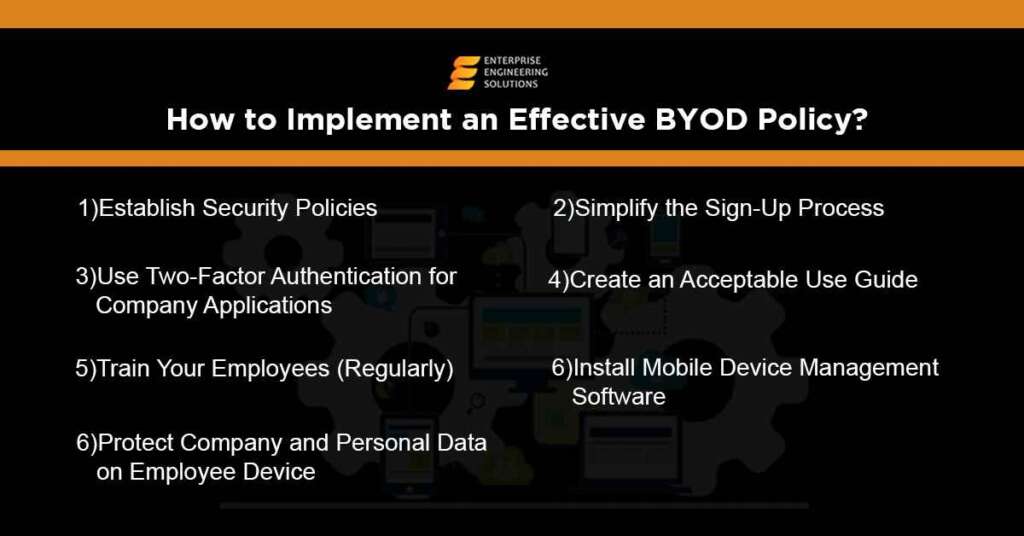
How To Implement an Effective BYOD Policy In Seven Steps
The advantages of an effective BYOD policy are difficult to resist. However, some companies that experience data breaches get attacked using employee-owned devices. Therefore, you need a policy underlining all potential problems and assuring convenience. Poorly planning the implementation of BYOD can be even more costly to businesses. It may cause excessive expenditure and requirements for IT support.
Consider using the following steps to structure and implement a BYOD policy that will be effective in keeping your teams productive:
Two-Factor Authentication
Two-factor authentication helps prevent hackers from infiltrating business applications by blocking unverified access to user accounts. Data is kept secure by requiring secondary authentication to verify a login attempt. Steps included in two-factor authentication involve security questions or using a verification code sent to your phone via text or email.
Create A Guide for Best Practices
Your BYOD policy should move hand-in-hand with an “Acceptable Use Policy.” It guides employees and ensures they know how to avoid distractions, and keeps your network secure. You must outline the specific applications and business data employees can remotely access from their devices and which remain restricted.
Don’t forget to highlight banned websites for connected devices and disciplinary action when someone violates company policies. Avoid blocking websites like YouTube and Facebook because it seems overly controlling for your employees’ devices. It would be best to have a good business user guide that is firm but not unnecessarily strict. It shows great trust in your team.
Mobile Device Management Applications
Mobile device management applications enable businesses to configure and manage all personal devices using a single application. Your IT department can determine the security and software configurations for all devices connected to your business’ network.
It is also easier to implement automatic data and intellectual property backups using cloud services. You can also scan for loopholes within your system and block risky devices. Application updates can also happen simultaneously using remote patching and security updates.
Outline Security Policies
Your employees can access business-sensitive information remotely from their local devices. Therefore, your BYOD policy needs to address security practices and potential challenges, including strict password requirements. It ensures that your data remains safe if a device falls into the wrong hands.
Your BYOD plan should also include:
- A Remote data wiping policy
- Data storage practices
- Minimum requirements for device security controls
- Mobile device Security Applications (if necessary)
- Timeouts and Inactivity limits
- Also, you may add more requirements for effective compliance regarding your line of business.
Regular Training for Employees
Businesses must conduct frequent training sessions to keep team members updated regarding BYOD policies and potential risks. Other effective training methods may include a comprehensive manual or permitting team members to schedule personal training sessions with the IT staff. It makes it easier for employees to learn how to use their devices for productivity, understand risks, and avoid them.
Simple Sign-Ups
Ensure that signing up for BYOD programs remains an easy process. Avoid making employees fill out too many forms or go through extensive approval processes. People should sign up within a few simple steps. And they should not be required to download too many applications to access information and operate effectively.
Company Data Protection on All Employee Devices
Alongside using a BYOD policy to protect business information and intellectual property, you must also safeguard team members’ data with a high level of privacy. Ensure that your device management software never exploits employees’ personal information.





