Statistics have shown over $17 billion in income is generated each quarter by cloud computing, which powers many of today’s internet-based apps and services. What individuals share and save, how they cooperate, and how they use distant apps are examples of how this technology is used in their daily life.
Introduction of Decentralized Approaches to Managing Data
Decentralized approaches are needed to fulfill digital business infrastructure requirements, according to businesses throughout the world. More than five billion IoT devices will require edge solutions by 2020. According to Business Insider Intelligence, Data and services are moved from one or more central nodes to the “edge”, which is frequently in contact with the end-users, using edge computing. To achieve this goal, edge computing employs a combination of peer-to-peer ad-hoc networking. It also uses local cloud computing. Grid computing. Fog computing.
Blockchain-Based Decentralized Approaches and FsMain Challenges
Since the early 1990s, there have been platforms for sharing computational resources. UC Berkeley’s SETI@home is an example of a scientific project in which individuals may contribute by running a free application that downloads and analyses radio telescope data. This dependency on central nodes to distribute and manage jobs, coupled with difficulties connected to suitable incentivization schemes for computing power suppliers and correct verifiability of the performed computation, are the primary drawbacks of such platforms at scale.
Ethereum emerges as a critical enabler of decentralized cloud solutions in this scenario. Because blockchain-based designs employ consensus and incentive systems to help distributed computing overcome some of the difficulties stated. Token-based node host compensation, for example, is not only a great way to encourage interested parties to put their resources online, but it also helps prevent bad players from taking advantage of the system.
Some of the Challenges Delineated are:
- Making sure resource suppliers have the proper incentive strategy in place by ensuring equitable revenue distribution
- Infrastructure scalability should be considered, given the present limits of blockchain infrastructure scalability.
- The computation must be verified (i.e., a provider claiming to have provided the service without effectively doing it). However, to be effective, reputation management strategies must strike the proper balance between reputation weight and market entrance costs.
- Oracles are not decentralized by nature. Use trustworthy oracles*. The trust problem might be mitigated via distributed oracle proposals. A malicious attack or other (standard) difficulties may give rise to the right to deletion of data.
- Many projects are exploring ways to integrate blockchain into distributed computing platforms. Use cases for blockchain in the decentralized cloud are described below.
Blockchain-Based Decentralized Cloud Solutions
Ankr
Data Centers will generate new revenue streams from their underutilized capacity by using Ankr, a decentralized cloud solution now under development. A high degree of service availability, easy integration, and secure communication will be required to achieve this goal. Containerization, cluster orchestration, and Trusted Execution Environments would be leveraged to achieve this goal (TEE).
Using a new consensus technique dubbed Proof of Useful Work (PoUW), the Ankr team can attain a high level of security while wasting minimum amounts of energy.
The figure below shows the fundamental component of Ankr’s mining strategy, which examines the critical participants in the system.
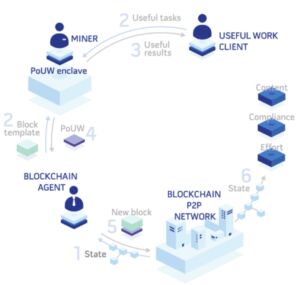
Due to the described method, the PoUW consensus achieves a high-security level while minimizing energy consumption.
Dfinity
A global supercomputer with “unlimited” capacity and processing power will be made available through the Dfinity project, a decentralized cloud solution. Crowd wisdom and classical AI technologies are used to freeze rogue smart contracts that undermine the interests of individuals utilizing the platform.
Since certain transactions may be altered and reverted with algorithmic approval, this is a different approach from projects like Bitcoin or Ethereum, where the rule “The Code is law” mandates that a user cannot edit or reverse the transaction once it has been completed.
The figure below shows the Dfinity consensus mechanism structure:
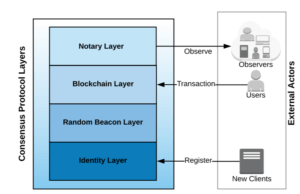
After a committee (a subset of all registered Clients) temporarily executes the protocol on behalf of all Clients, it assigned the ultimate execution to another Committee, which delegated it to another Committee.
While maintaining fairness and security, this technique allows the infrastructure to scale predictably.
Vocabulary Recognition Functions (VRF) give publicly verifiable evidence of their output’s accuracy without requiring a secret key.
Solana
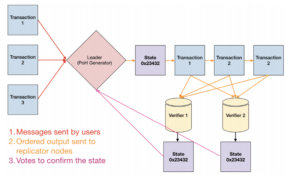
In the Solana project, the Proof of History idea is used to construct a unique blockchain architecture (PoH). PoH employs a verified delay function to provide the network a feeling of shared time that is not reliant on trust. The GPUs on Solana also handle transaction processing, a method that scales with Moore’s Law.
An integrated circuit with many transistors is said to double its transistor count every two years, providing a significant increase in computing capacity. Together with a Proof of Stake consensus process, this mechanism can make the infrastructure extremely scalable.
It is possible to use the infrastructure for a variety of purposes, such as decentralized cloud computing.
The Solana transaction flow is shown in the figure:
New decentralized cloud providers are expected to enter the market in the future, competing with established companies by delivering new services. Several additional projects in development have been in development for 2–3 years and are currently in testing phases.
Because decentralized cloud architectures based on blockchain technology are still in their infancy, essential criteria such as quality of service and performance and scalability and security will be crucial in the long term for these projects to develop economically.





